I installed a Solana browser wallet last week to test how smooth onboarding truly is. It felt snappy on Chrome and Brave but there were odd edge cases. Whoa, that surprised me. At first I thought the UI would guide even non-crypto folks through seed phrases and network settings with ease, but then I hit a prompt where the language was ambiguous enough that I hesitated and had to Google for clarity. My instinct said something was off in the UX copy.
Seriously, it surprised me. If you’re new to wallets, the drop-down menus and cluster settings are bewildering. Extensions try to be helpful but often hide advanced options behind small icons. Initially I thought the issue was solely about copywriting and onboarding, but then realized that permission models and RPC choices actually change how dapps behave across networks which is a deeper problem. The result was hesitation and occasional task failure for me.
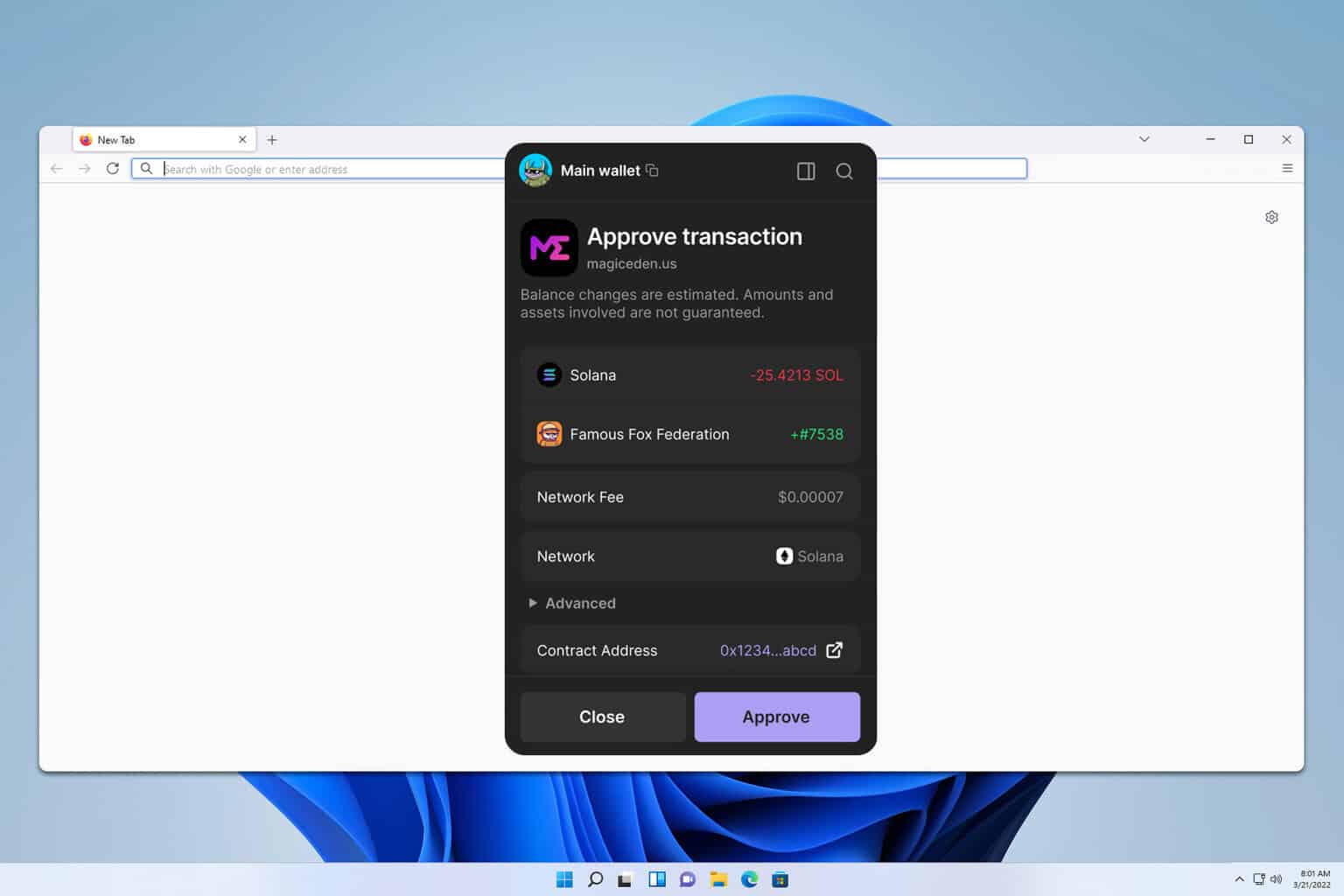
Okay, so check this out—Phantom makes Solana feel approachable. Wow — that helps a lot. My instinct said this is what mainstream users need. But when you start interacting with NFT marketplaces or mixed-signature smart contracts, you run into subtle UX choices like auto-approving collectors or confusing transaction fees that can lead to accidental approvals and real losses — and that part bugs me. I’m biased, but I prefer clearer permission prompts and better defaults.
Actually, wait—let me rephrase that. From a developer standpoint, wallet APIs on Solana are straightforward. They can vary a lot in how signing requests appear. On one hand some extensions show full transaction details before asking for approval, though actually others compress that information to a few lines which, in practice, hides critical approvals behind terse labels that many users just click through. That behavior is very very important to fix for safety.
Practical safety: how I test and where to fetch the extension
Check this out—some dapps request ‘Approve’ for entire collections and users accept. Really? That’s scary. Phantom and similar wallets offer guardrails, but settings are buried or off by default. So I started customizing defaults and tested NFT purchases across multiple marketplaces, logging prompts and approvals, and what I found surprised me: some flows suggested allowances that would let a contract transfer many tokens without per-item confirmation. My takeaway was that wallets need smarter heuristics and clearer language.
Whoa, seriously, this happened. I documented examples where multi-approval flows looked like single payments. Developers can help by requesting minimal scopes and by explaining intents inline. On the security side, hardware wallet integration and explicit revocation flows should be easier to access, because revoking token allowances after a wide-permission approval is currently too obscure for most users and that creates long tail risk. I’m not 100% sure how to balance defaults and usability, though it’s crucial.
Here’s what bugs me about current wallet extension ecosystems. Hmm, interesting, right? Many extensions prioritize speed and minimal friction, which is good for adoption. Yet speed without clear user agency leads to consent fatigue where people click through permission dialogs, and that undermines the promise of self-custody in the long run, especially for high-value NFTs or novel token standards. We need better defaults, accessible revocations, and clearer signer previews.
Whoa! That was real. For users who care, Phantom’s UX is a solid starting point. It balances simplicity and advanced options to lower the barrier for collectors and devs. If you trust it and want to test, use curated links or add it from the official site; don’t click random downloads, and always verify the extension’s permissions and origin before connecting your primary account, because social engineering stays a real threat. One place to grab it is via a verified installer.
Get it right — the safer route
If you want to try Phantom, get it from a trusted source and read permissions. Seriously, take a second. I usually test on a spare account and move small amounts first. Start at the official installer: phantom wallet download extension and verify the domain before installing. Treat browser extensions like a keyring — keep the minimum amount of funds in hot wallets, use hardware for large holdings, and regularly audit connected sites because even small UI affordances can hide massive privileges if left unchecked.
Okay, I’m done. In practice, wallets are improving but not perfect yet. Phantom offers a pragmatic middle path with decent defaults and room for clearer permissions. Initially I thought wallets would converge faster on a small set of patterns, but the ecosystem’s creativity and competing design choices mean the UX conversations will keep evolving, which is both exciting and a little maddening. If you’re curious, test on devnets and keep learning.
FAQ
Is a browser extension wallet safe for NFTs?
Short answer: usually, if you follow safe practices and verify what you’re approving. Test purchases on devnets, use a spare wallet for experimenting, and revoke approvals when you can.
How should I manage approvals and allowances?
Prefer minimal-scoped approvals and check the transaction preview closely; somethin’ simple like a mislabeled approval can give far-reaching permissions. Use hardware wallets for sizeable holdings and revisit connected dapps regularly to revoke unused allowances.